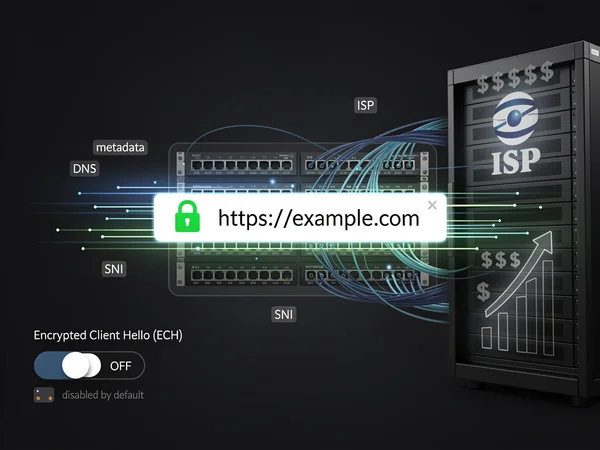
For years, internet users have been told that the small padlock icon in their browser’s address bar represents the gold standard of online privacy. That visual indicator of HTTPS encryption has become synonymous with secure browsing, leading millions to believe their online activities remain private from prying eyes. However, a critical gap in this security framework has emerged that even the most privacy-conscious users often overlook: their Internet Service Providers can still monitor nearly every website they visit, regardless of HTTPS encryption.
This revelation challenges the fundamental assumptions many users hold about online privacy. While HTTPS successfully encrypts the content of communications between browsers and websites—preventing ISPs from reading emails, viewing passwords, or intercepting sensitive data—it does nothing to hide which websites users are visiting. The distinction between content privacy and browsing privacy has become increasingly important as ISPs face fewer regulatory restrictions on data collection and monetization practices.
Advertisement
article-ad-01According to MakeUseOf , the solution to this privacy gap lies in a browser setting that remains disabled by default in most major browsers: Encrypted Client Hello, or ECH. This technology represents the latest evolution in the ongoing battle between user privacy and network surveillance, offering a way to close the loophole that has existed since the inception of encrypted web traffic.
The Technical Reality Behind ISP Surveillance
Understanding how ISPs can monitor browsing activity despite HTTPS encryption requires examining the technical mechanics of how internet connections are established. When a user types a website address into their browser, multiple steps occur before any encrypted connection is formed. First, the browser must translate the human-readable domain name into an IP address through a DNS lookup. This query, sent in plain text in most configurations, immediately reveals to the ISP which website the user intends to visit.
Even after the DNS lookup completes and the browser initiates an HTTPS connection, another vulnerability emerges during the TLS handshake process. This initial negotiation between the browser and web server includes a field called Server Name Indication (SNI), which explicitly states the hostname of the website being accessed. The SNI field was introduced to solve a technical problem: allowing multiple websites to share a single IP address while still using HTTPS. However, this solution created a privacy trade-off, as the SNI is transmitted in plain text, visible to anyone monitoring the connection—including ISPs.
How Internet Providers Capitalize on Browsing Data
The ability of ISPs to monitor browsing habits has significant commercial implications. Internet service providers operate in an increasingly competitive market where traditional connectivity services have become commoditized. To enhance revenue streams, many ISPs have turned to data monetization strategies that leverage the vast amounts of information flowing through their networks. Browsing histories represent valuable datasets that can be analyzed, aggregated, and sold to advertisers, data brokers, and marketing firms.
The regulatory environment surrounding ISP data collection has shifted dramatically in recent years. In 2017, the U.S. Congress voted to repeal broadband privacy rules that would have required ISPs to obtain explicit consent before selling customer data. This regulatory rollback removed significant barriers to ISP data monetization, creating a framework where browsing histories could be treated as a commercial asset rather than private information requiring protection.
Encrypted Client Hello: The Technical Solution
Encrypted Client Hello represents a fundamental redesign of how browsers initiate secure connections. Previously known as Encrypted SNI (ESNI), ECH extends encryption to cover the entire initial handshake process, including the critical Server Name Indication field. When ECH is enabled, the browser encrypts the hostname information before sending it to the web server, rendering it unreadable to intermediaries like ISPs.
The implementation of ECH requires cooperation from both browsers and websites. Major browser developers including Mozilla, Google, and Apple have integrated ECH support into their products, though it often remains disabled by default. On the server side, websites must configure their infrastructure to support ECH, which involves updating TLS configurations and ensuring compatibility with the latest encryption standards. Cloudflare, a major content delivery network provider, has been instrumental in promoting ECH adoption by enabling support across its extensive network of websites.
Enabling ECH Across Different Browsers
For Firefox users, enabling ECH requires navigating to the browser’s configuration settings by typing “about:config” in the address bar. Users must then search for “network.dns.echconfig.enabled” and toggle the setting to true. Firefox has been at the forefront of privacy-enhancing technologies, and Mozilla has indicated plans to eventually enable ECH by default for all users. The browser also requires DNS-over-HTTPS to be enabled for ECH to function properly, creating a comprehensive privacy solution.
Chrome users face a slightly different process, as Google has implemented ECH support but keeps it disabled in standard configurations. Enabling the feature requires accessing Chrome’s experimental flags by typing “chrome://flags” in the address bar and searching for “Encrypted ClientHello.” The setting must be changed from “Default” to “Enabled,” followed by a browser restart. However, users should note that experimental flags can change or be removed in future Chrome updates, and Google’s approach to ECH deployment has been more cautious than Mozilla’s.
The Limitations and Complementary Technologies
While ECH represents a significant advancement in browsing privacy, it does not provide complete anonymity or eliminate all forms of ISP monitoring. Internet providers can still observe the IP addresses users connect to, which can reveal website visits when sites use dedicated IP addresses. Additionally, ECH only protects the initial connection; subsequent traffic patterns, timing, and data volumes can potentially be analyzed through sophisticated traffic analysis techniques.
To achieve more comprehensive privacy protection, security experts recommend combining ECH with other privacy-enhancing technologies. DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT) encrypts DNS queries, preventing ISPs from monitoring domain lookups. Virtual Private Networks (VPNs) route all internet traffic through encrypted tunnels, hiding both destinations and content from ISPs. The Tor network provides even stronger anonymity by routing traffic through multiple encrypted relays, though at the cost of significantly reduced browsing speeds.
The Broader Implications for Internet Privacy
The development and deployment of ECH reflects a broader philosophical debate about the nature of privacy in the digital age. On one side, privacy advocates argue that individuals have a fundamental right to browse the internet without surveillance, even from the companies providing their connectivity. They contend that the ability of ISPs to monitor and monetize browsing data creates perverse incentives that undermine user trust and enable potential abuses.
Opposing this view, some ISPs and telecommunications companies argue that network visibility serves legitimate purposes beyond data monetization. They claim that monitoring traffic patterns helps identify and mitigate security threats, manage network congestion, and comply with legal obligations. The tension between these perspectives has shaped regulatory debates and influenced the pace of privacy technology adoption.
Industry Adoption and Future Developments
The path toward widespread ECH adoption faces several obstacles. Website operators must update their server configurations, which requires technical expertise and may introduce compatibility concerns with older systems. Browser developers must balance privacy enhancements against potential performance impacts and user experience considerations. Additionally, some network administrators and enterprise IT departments have expressed concerns about ECH limiting their ability to monitor and secure corporate networks.
Despite these challenges, momentum appears to be building toward broader ECH implementation. Major content delivery networks have pledged support for the technology, and browser vendors have included ECH in their long-term privacy roadmaps. Industry observers expect that as the technology matures and proves its reliability, default-enabled ECH will become standard across major browsers, similar to how HTTPS has evolved from an optional security measure to the expected baseline for all websites.
Practical Steps for Enhanced Privacy
For users seeking to protect their browsing privacy immediately, enabling ECH represents one component of a comprehensive privacy strategy. Beyond browser settings, individuals should consider their choice of DNS provider, as many ISPs default to using their own DNS servers that log all queries. Switching to privacy-focused DNS services like Cloudflare’s 1.1.1.1 or Quad9 can prevent ISPs from monitoring domain lookups, especially when combined with DoH or DoT protocols.
Privacy-conscious users should also evaluate their overall threat model and determine which privacy tools align with their specific needs. Casual users concerned primarily about ISP data collection may find that ECH and encrypted DNS provide sufficient protection. Those facing more significant privacy risks—such as journalists, activists, or individuals in countries with restrictive internet policies—should consider more robust solutions including VPNs or Tor. Understanding the strengths and limitations of each technology enables informed decision-making about privacy protection strategies.
The revelation that HTTPS alone provides incomplete privacy protection highlights the evolving nature of internet security and the importance of staying informed about emerging privacy technologies. As the digital economy increasingly relies on data collection and analysis, users who understand the technical realities of online privacy gain the power to make conscious choices about their digital footprints. Encrypted Client Hello may not be a household term, but its potential impact on internet privacy could prove as significant as the widespread adoption of HTTPS itself, marking another step toward a more private and secure internet for all users.

LEAVE A REPLY
Your email address will not be published