- Home
- IT Management
IT Management focuses on governance, security, infrastructure, and operations—helping teams run reliable systems, reduce risk, and align technology with business goals.
IT Management
Apple’s Precision Location Throttling: How Carriers Lost Their Grip on iPhone User Data
Apple has quietly restricted wireless carriers' access to precise iPhone location data, forcing telecommunications companies to rely on less accurate tracking methods. This move reshapes industry power dynamics while advancing Apple's privacy-first positioning.
IT ManagementNorth Korean Malware Fractures Into Three-Headed Hydra as Pyongyang Refines Cyber Arsenal
North Korean hackers have evolved a dangerous malware strain into three distinct variants that work together to maximize damage while evading detection. This fragmentation strategy represents a significant escalation in Pyongyang's cyber capabilities, targeting financial institutions and critical infrastructure worldwide.
IT ManagementAmerica’s Fiber-Optic Gold Rush Stalls as Skilled Workers Vanish From the Field
America's $65 billion push to build fiber-optic infrastructure faces an unexpected obstacle: a severe shortage of skilled workers. With 178,000 positions unfilled by 2032, the labor crisis threatens to delay both universal broadband access and the AI revolution that depends on it.
IT ManagementShinyHunters Escalates Cyber Extortion Through Sophisticated Voice Phishing Blitz Targeting Corporate America
ShinyHunters cybercrime syndicate launches sophisticated vishing campaign targeting hundreds of corporations, combining data breaches from Match.com, Bumble, and Panera Bread with social engineering tactics. The SLSH campaign represents dangerous evolution in cyber extortion, exploiting human vulnerabilities alongside technical systems.
IT ManagementWhy Security Awareness Training Fails: The Shift to Human Risk Management in Corporate Cybersecurity
Despite billions spent on security awareness training, human error remains the leading cause of breaches. Human risk management offers a data-driven alternative, focusing on behavioral change rather than knowledge transfer to address cybersecurity's most persistent vulnerability.
IT ManagementThe Confidence Crisis: Why Nearly 60% of Security Chiefs Say Their Companies Can’t Handle a Cyberattack
Despite record cybersecurity spending, 58% of CISOs believe their organizations are unprepared for cyberattacks. Four fundamental challenges—budget misalignment, organizational silos, talent shortages, and inadequate executive support—create a dangerous gap between security investments and actual readiness, leaving companies vulnerable despite their best intentions.
IT ManagementPalo Alto Networks Races to Shield Corporate America From Quantum Computing’s Cryptographic Threat
Palo Alto Networks launches quantum-safe security solution providing real-time cryptographic visibility to help enterprises protect against future quantum computing threats. The platform enables automated discovery and risk assessment of vulnerable encryption systems across global IT infrastructure.
IT ManagementWhen Innovation Becomes Paralysis: Why Security Chiefs Are Drowning in AI Possibilities
Chief Information Security Officers face an unexpected challenge: paralysis from AI abundance. Despite pressure to adopt artificial intelligence tools, security leaders struggle with vendor proliferation, integration nightmares, skills gaps, and regulatory uncertainty that create decision-making gridlock in enterprise security.
IT ManagementWhen Cybersecurity Leadership Bypasses Its Own Rules: The CISA ChatGPT Incident
A senior CISA official uploaded sensitive government contracting documents to public ChatGPT, bypassing DHS-approved AI tools. The incident exposes critical gaps between federal cybersecurity policy and practice, raising questions about enforcement, training, and the challenges agencies face in securely adopting generative AI technologies.
IT ManagementThe Death of the Perimeter: Why Identity-Based Security Is Replacing Traditional Firewalls
Traditional perimeter defenses are becoming obsolete as organizations shift to identity-based security models. The new paradigm verifies user identity continuously rather than granting trust based on network location, fundamentally transforming how enterprises protect assets in an era of remote work and cloud computing.
IT ManagementSandworm’s Shadow: How Russia’s Most Dangerous Hacking Group Targeted Poland’s Electric Infrastructure
ESET researchers have attributed December 2024 cyberattacks on Poland's electricity grid to Sandworm, Russia's elite GRU hacking unit. The operation highlights critical infrastructure vulnerabilities and escalating Russian hybrid warfare against NATO members, raising urgent questions about collective defense and deterrence strategies.
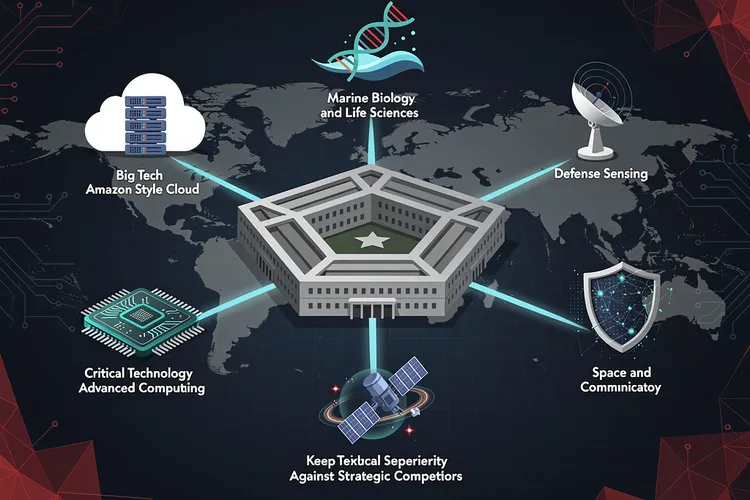
IT ManagementPentagon’s New Technology Chiefs Signal Major Shift in Defense Innovation Strategy
The Pentagon's Chief Technology Officer has selected six defense technology veterans with diverse backgrounds—from Amazon executives to marine biologists—to lead Critical Technology Areas, signaling a major shift in how the Defense Department approaches innovation and maintains technological superiority against strategic competitors.
IT ManagementMost Popular
- Formae’s Multi-Cloud Leap: Platform Engineering Labs Arms Builders Against IaC Gridlock
- Sky47’s Sovereign Surge: Pakistan’s Massive AI Cloud Bet
- Cloud’s Complexity Trap: How Tool Overload and AI-Wielding Attackers Are Fracturing Security Defenses
- NordVPN’s Sixth Consecutive Audit Validates Zero-Logs Promise as Privacy Scrutiny Intensifies
- Upwind’s Runtime Revolution: $250M Fuels $1.5B Cloud Security Unicorn
Advertisement
category-ad-01